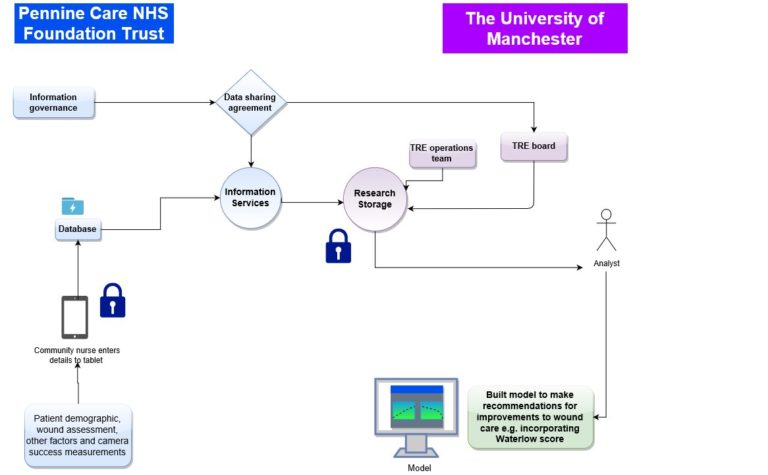
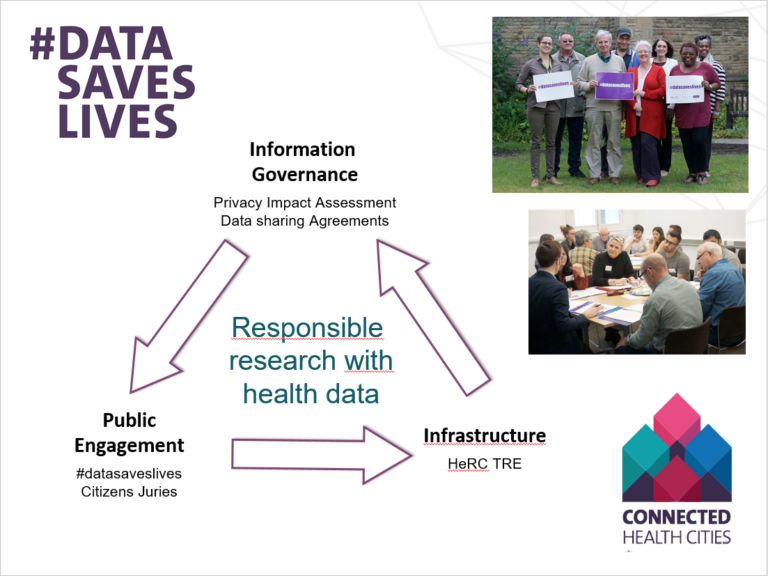
The Health eResearch Centre, based in the School of Health Sciences, keeps its data safe using the Trustworthy Research Environment (also known as the HeRC TRE), a data analytics resource certified. The TRE is used in a large number of the Health eResearch Centre and Connected Health Cities’ (CHC’s) research projects, such as CHC’s exploration of wound care data, a project that uses existing wound care records to improve wound assessment and treatment. The TRE is also used in various projects that are external to HeRC and CHC, and is available to host research on behalf of any organisation.
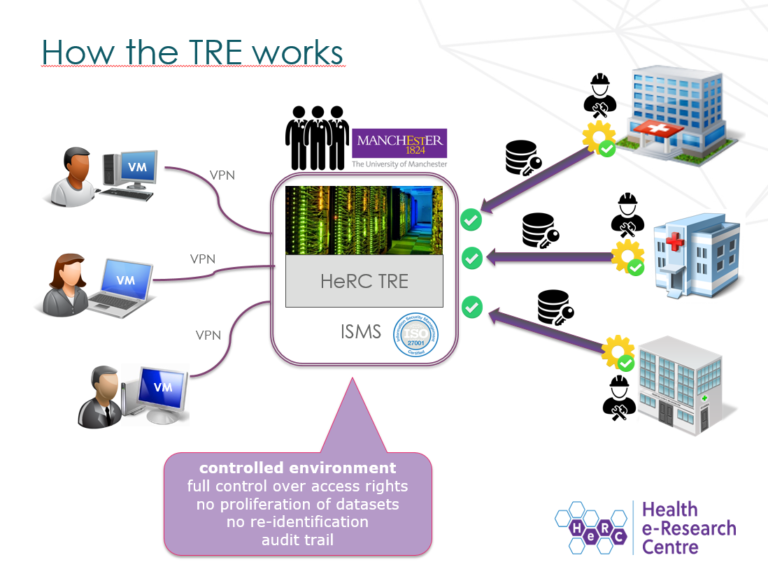
The TRE uses a number of strict security controls to prevent unauthorised access and misuse of data. For example, data protected by the TRE is encrypted in transit and at rest, and can only be accessed via virtualised workstations which are isolated from the internet, minimising the risk of data interception. Connections to these virtual workstations is secured via a VPN service and 2-Factor authentication. Each virtual workstation belongs solely to a single project, which further reduces the risk of interception: only the researchers working on that project can access the corresponding data.
The TRE is the only data analytics resource at The University of Manchester that offers a connection to the NHS’s Health and Social Care Network (HSCN, formerly known as N3), a secure, private network that allows researchers quick and efficient access to NHS data, and which allows The University of Manchester to share data and web-based services with staff at the NHS. Some of the TRE’s data storage, virtual workstations and application servers are hosted on the HSCN, which makes it possible to conduct data processing and analytics without the need to remove the data from the HSCN.
By incorporating some of the TRE infrastructure within the HSCN, researchers can access higher quality, more detailed data. For example, Patient Identifiable Data can be shared using the HSCN, allowing researchers a wider scope of data. Moreover, the TRE board oversees all applications to check that each project has necessary permissions to access this data, referring to the ‘Five safes’: in order to be granted access to data, the project, people involved, data, facility settings and project outputs must all be deemed safe, ethical and responsible.